
Top Palo Alto Networks Alternatives: The Complete Guide to Network Security Solutions
Organizations worldwide rely on robust network security platforms to protect their digital assets. While Palo Alto Networks has established itself as a market leader, many enterprises are exploring alternative solutions that better align with their specific requirements, budget constraints, or architectural preferences.
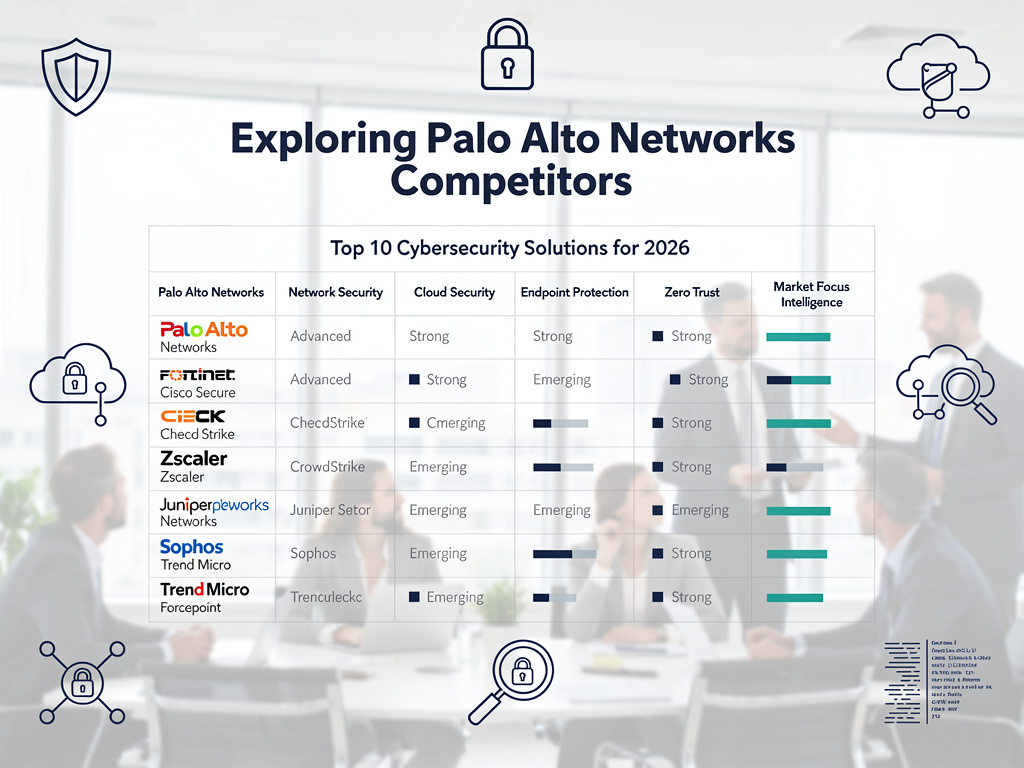
This comprehensive analysis examines ten leading alternatives to Palo Alto Networks. Each solution offers unique strengths in areas such as cloud-native security, SD-WAN integration, threat prevention, and cost-effectiveness. From established players like Fortinet and Cisco to innovative cloud-first platforms like Zscaler and Cloudflare, these alternatives cater to diverse organizational needs.
We’ll evaluate each platform using consistent criteria including security capabilities, scalability, ease of deployment, pricing models, and integration features. This detailed comparison will help security professionals make informed decisions when selecting the optimal network security solution for their organization in 2026.
Why Organizations Seek Palo Alto Networks Alternatives
Enterprise security teams increasingly evaluate alternatives to Palo Alto Networks for several compelling reasons. Cost optimization remains a primary driver, as organizations seek solutions that deliver comparable security effectiveness at more competitive price points.
Complex deployment requirements often push organizations toward more streamlined alternatives. Many enterprises find Palo Alto’s configuration complexity challenging, especially when rapid deployment is critical. Simplified management interfaces and automated security policies have become essential requirements.
Cloud-first architectures demand security solutions built specifically for modern infrastructure. Traditional on-premises-focused platforms struggle to provide the agility and scalability that cloud-native environments require. Organizations migrating to hybrid or multi-cloud architectures need security platforms that seamlessly integrate across diverse environments.
Vendor diversification strategies also influence platform selection. Security teams prefer avoiding single-vendor dependencies, especially for critical infrastructure components. This approach reduces risk while providing negotiation leverage during contract renewals.
Performance requirements vary significantly across industries and use cases. Some organizations need ultra-low latency solutions, while others prioritize maximum throughput. Specialized alternatives often excel in specific performance dimensions where general-purpose platforms may fall short.
Evaluation Criteria for Network Security Platform Comparison
Comprehensive evaluation requires consistent assessment criteria across all platforms. Our analysis focuses on six core dimensions that directly impact organizational success and security effectiveness.
Security Capabilities encompass threat prevention, detection accuracy, and response automation. Advanced threat intelligence integration, machine learning-driven analysis, and behavioral analytics capabilities determine each platform’s effectiveness against sophisticated attacks.
Scalability and Performance measure how solutions handle growing traffic volumes and expanding organizational requirements. This includes throughput capacity, latency impact, and ability to scale across multiple locations or cloud regions.
Deployment and Management evaluate implementation complexity, ongoing administrative overhead, and operational efficiency. User-friendly interfaces, automation capabilities, and centralized management features significantly impact total cost of ownership.
Integration Ecosystem assesses compatibility with existing security tools, IT infrastructure, and business applications. Robust API support, pre-built connectors, and standards compliance enable seamless integration workflows.
Pricing and Licensing examine cost structures, licensing models, and long-term financial implications. Transparent pricing, flexible licensing options, and predictable cost scaling help organizations budget effectively.
Vendor Support and Reliability consider technical support quality, platform stability, and vendor financial health. Responsive support teams, comprehensive documentation, and proven track records ensure successful long-term partnerships.
Cato Networks: Comprehensive SASE Platform
Cato Networks pioneered the Secure Access Service Edge (SASE) approach, combining network and security functions into a unified cloud platform. Their global backbone infrastructure provides consistent performance and security policies across all locations.
The platform excels in simplifying network architecture by replacing multiple point solutions with integrated SASE capabilities. Organizations eliminate the complexity of managing separate SD-WAN, firewall, secure web gateway, and CASB solutions. This consolidation reduces vendor management overhead while improving security posture.
Security Capabilities: Cato’s threat prevention combines signature-based detection with advanced behavioral analytics. Their Security Research Labs continuously update threat intelligence feeds, ensuring protection against emerging attack vectors. The platform provides comprehensive visibility into all network traffic, including encrypted communications.
Scalability and Performance: The global Points of Presence (PoPs) network ensures low-latency connectivity regardless of user location. Cato’s cloud-native architecture automatically scales resources based on demand, eliminating capacity planning challenges. Organizations can rapidly deploy new locations without hardware procurement delays.
Deployment and Management: Zero-touch provisioning capabilities enable rapid site deployment with minimal technical expertise. The centralized management console provides unified policy enforcement across all network edges. Automated configuration ensures consistent security policies without manual intervention.
Integration Ecosystem: Cato supports standard networking protocols and provides APIs for custom integrations. However, the platform’s comprehensive nature may reduce integration needs compared to best-of-breed approaches. Organizations should evaluate whether Cato’s integrated approach aligns with their preferred vendor diversity strategies.
Pricing and Licensing: Subscription-based pricing includes all platform capabilities without per-feature charges. This predictable cost structure simplifies budgeting but may result in paying for unused features. Organizations should carefully assess which capabilities they actually need versus Cato’s comprehensive offering.
Vendor Support and Reliability: Cato provides 24/7 support with guaranteed response times based on service level agreements. Their Network Operations Center continuously monitors platform performance and proactively addresses potential issues. The company’s strong financial position and continued growth indicate long-term viability.
Fortinet: Enterprise-Grade Security Fabric
Fortinet’s Security Fabric approach delivers integrated protection across the entire attack surface. Their custom ASIC technology provides industry-leading performance at competitive price points, making them attractive for bandwidth-intensive environments.
FortiGate firewalls form the foundation of Fortinet’s ecosystem, supporting deployment models from small offices to large data centers. The platform’s strength lies in its comprehensive security portfolio and deep integration between security functions.
Security Capabilities: FortiGuard Labs provides real-time threat intelligence updates across the entire Fortinet ecosystem. Advanced threat protection includes sandboxing, machine learning-based detection, and AI-powered security analytics. The Security Fabric enables automatic threat response and policy enforcement across all connected security devices.
Scalability and Performance: Custom security processing units (SPUs) deliver consistent performance even under high traffic loads. Hardware-accelerated encryption and decryption maintain network speeds while providing comprehensive inspection capabilities. Fortinet supports deployment scaling from small branch offices to large enterprise data centers.
Deployment and Management: FortiManager provides centralized management for thousands of FortiGate devices. Template-based configuration ensures consistent policy deployment across all locations. However, initial configuration complexity may require specialized training or professional services engagement.
Integration Ecosystem: The Fortinet Security Fabric integrates with hundreds of third-party security vendors through the Open Ecosystem initiative. Fabric connectors enable automated threat sharing and coordinated response across diverse security tools. This approach supports organizations with existing security investments.
Pricing and Licensing: Fortinet’s competitive pricing strategy provides excellent price-performance ratios, especially for high-throughput requirements. Bundled licensing options include multiple security services at attractive rates. Organizations should carefully evaluate long-term licensing costs as requirements evolve.
Vendor Support and Reliability: Fortinet provides comprehensive support options including 24/7 technical assistance and proactive monitoring services. Their established market presence and continued R&D investment demonstrate long-term commitment to platform evolution. Regular firmware updates address security vulnerabilities and add new capabilities.
Zscaler: Cloud-First Zero Trust Security
Zscaler revolutionized network security by delivering protection entirely through cloud services. Their Zero Trust Exchange eliminates traditional network perimeters, treating every connection as potentially untrusted until verified.
The platform excels for organizations embracing digital transformation initiatives and cloud-first strategies. Zscaler’s architecture aligns naturally with modern work patterns, including remote workforce enablement and cloud application adoption.
Security Capabilities: Advanced threat protection leverages cloud-scale analytics and machine learning to identify sophisticated attacks. The platform inspects all traffic in real-time, including SSL/TLS encrypted communications. Continuous risk assessment adapts security policies based on user behavior and context.
Scalability and Performance: Global cloud infrastructure automatically scales to handle traffic spikes without capacity planning. Users connect to the nearest Zscaler data center, minimizing latency impact. The cloud-native architecture eliminates hardware refresh cycles and capacity constraints.
Deployment and Management: Agent-based deployment enables rapid user onboarding without network infrastructure changes. Policy management through the centralized portal supports granular controls based on user, application, and risk factors. However, organizations may need to adapt existing network architecture approaches.
Integration Ecosystem: Zscaler provides extensive API support and pre-built integrations with leading identity providers, SIEM platforms, and endpoint protection solutions. The platform works seamlessly with cloud applications while providing visibility into shadow IT usage patterns.
Pricing and Licensing: User-based subscription pricing scales with organizational growth. Premium features require higher-tier licensing, which may increase costs for advanced capabilities. Organizations should evaluate total cost including potential network infrastructure changes.
Vendor Support and Reliability: Zscaler offers comprehensive support options with global coverage. Their cloud platform provides inherent redundancy and disaster recovery capabilities. The company’s continued innovation and market growth demonstrate strong financial stability.
Netskope: Data-Centric Cloud Security
Netskope specializes in data protection across cloud applications and web traffic. Their platform provides granular visibility and control over cloud usage, making them particularly strong for organizations with extensive SaaS application portfolios.
The NewEdge network delivers optimal performance for cloud application access while maintaining comprehensive security inspection. Netskope’s approach balances security requirements with user experience demands.
Security Capabilities: Advanced data loss prevention (DLP) protects sensitive information across all cloud applications and web traffic. The platform uses machine learning to identify risky user behaviors and automate threat response. Real-time coaching helps users make secure decisions without blocking productivity.
Scalability and Performance: The global NewEdge infrastructure provides consistent performance regardless of user location or cloud application deployment. Intelligent traffic routing optimizes paths to cloud services while maintaining security inspection. Netskope supports rapid scaling for organizations with growing cloud adoption.
Deployment and Management: Multiple deployment options include agent-based, proxy-based, and API-driven approaches. The unified management console provides comprehensive visibility across all protected cloud services. Policy templates accelerate deployment for common use cases and compliance requirements.
Integration Ecosystem: Netskope offers extensive API support and pre-built connectors for hundreds of cloud applications. Integration with identity providers enables context-aware access controls. However, the platform’s cloud focus may require additional solutions for comprehensive network security coverage.
Pricing and Licensing: Subscription pricing varies based on protected users and enabled features. Cloud application connectors may require separate licensing, potentially increasing costs for organizations with diverse cloud portfolios. Total cost depends significantly on specific feature requirements and usage patterns.
Vendor Support and Reliability: Netskope provides global support with cloud security specialists. Their platform design includes redundancy and high availability features. Continued market growth and customer expansion demonstrate platform effectiveness and vendor stability.
Versa Networks: SD-WAN Security Integration
Versa Networks delivers integrated SD-WAN and security capabilities through their SASE platform. Their approach combines networking and security functions while maintaining flexibility for diverse deployment requirements.
The platform excels in simplifying branch office connectivity while providing comprehensive threat protection. Versa’s architecture supports both cloud and on-premises deployment models, accommodating various organizational preferences.
Security Capabilities: Integrated next-generation firewall capabilities provide application awareness and intrusion prevention. Advanced threat detection leverages machine learning and behavioral analytics to identify sophisticated attacks. The platform includes secure web gateway and DNS protection features.
Scalability and Performance: Software-defined architecture enables rapid scaling across multiple locations and cloud regions. Performance optimization features ensure consistent application experience over diverse network connections. Versa supports deployment scaling from small branches to large enterprise environments.
Deployment and Management: Unified orchestration simplifies policy management across networking and security functions. Zero-touch provisioning enables rapid site deployment with minimal local technical support. However, initial configuration may require specialized expertise for optimal performance.
Integration Ecosystem: Versa provides API support and integration capabilities with leading security and networking vendors. The platform supports standard protocols and interfaces for seamless ecosystem integration. Organizations can leverage existing security investments while adding SD-WAN capabilities.
Pricing and Licensing: Subscription-based pricing includes both networking and security capabilities. Bundled licensing may provide cost advantages compared to separate best-of-breed solutions. Organizations should evaluate whether integrated functionality meets their specific requirements versus specialized alternatives.
Vendor Support and Reliability: Versa offers comprehensive support options including professional services for deployment and optimization. The company’s focus on customer success ensures ongoing platform optimization. Regular updates add new capabilities and address security vulnerabilities.
Cisco: Comprehensive Security Architecture
Cisco’s security portfolio spans network infrastructure, endpoint protection, and cloud security. Their integrated approach leverages decades of networking expertise while embracing modern security paradigms.
SecureX platform provides unified security management across Cisco’s diverse security portfolio. This integration enables coordinated threat response and simplified security operations for large enterprise environments.
Security Capabilities: Talos threat intelligence provides industry-leading threat research and protection updates. Advanced malware protection includes sandboxing, behavioral analysis, and machine learning-based detection. The platform offers comprehensive visibility across network, endpoint, and cloud environments.
Scalability and Performance: Enterprise-grade hardware platforms support high-throughput requirements with consistent performance. Cloud-delivered security services enable rapid scaling without infrastructure investment. Cisco supports deployment architectures from small offices to large data centers and cloud environments.
Deployment and Management: Cisco Defense Orchestrator provides centralized management for firewall policies and configurations. However, the complexity of Cisco’s security portfolio may require specialized training and expertise. Professional services support helps organizations optimize deployment and ongoing management.
Integration Ecosystem: Extensive partnership ecosystem enables integration with third-party security and networking solutions. Standard protocols and APIs support custom integrations and automated workflows. However, organizations may find vendor lock-in concerns with heavily integrated Cisco environments.
Pricing and Licensing: Enterprise licensing provides comprehensive feature access with predictable annual costs. However, Cisco’s pricing may be higher than specialized alternatives for specific use cases. Organizations should carefully evaluate total cost including hardware, licensing, and support components.
Vendor Support and Reliability: Cisco provides world-class technical support with global coverage and local expertise. Their market leadership position and continued R&D investment ensure long-term platform evolution. Extensive partner ecosystem provides additional deployment and support options.
Cloudflare: Edge-Based Security Services
Cloudflare’s global edge network delivers security services at internet scale. Their approach protects applications and networks by filtering traffic before it reaches organizational infrastructure.
The platform excels in protecting web applications and APIs from various attack vectors. Cloudflare’s massive global network provides inherent DDoS protection while maintaining application performance.
Security Capabilities: Web Application Firewall (WAF) protects against OWASP Top 10 threats and zero-day vulnerabilities. Bot management identifies and mitigates automated attacks while allowing legitimate traffic. Zero Trust Network Access provides secure remote access without traditional VPN complexity.
Scalability and Performance: Global anycast network automatically routes traffic to optimal edge locations. Infinite scalability handles traffic spikes without capacity planning or infrastructure investment. Performance optimization features improve application response times while maintaining security protection.
Deployment and Management: DNS-based deployment enables rapid protection activation without infrastructure changes. Intuitive dashboard provides easy policy configuration and traffic analytics. However, comprehensive network security may require combining multiple Cloudflare services.
Integration Ecosystem: Robust API platform enables custom integrations and automated security workflows. Cloudflare Workers allows organizations to deploy custom security logic at the edge. Integration with identity providers supports context-aware access controls.
Pricing and Licensing: Usage-based pricing scales with organizational requirements and traffic volumes. Free tier provides basic protection for small organizations or development environments. Enterprise features require higher-tier subscriptions which may increase costs for advanced capabilities.
Vendor Support and Reliability: Global support organization provides 24/7 assistance for enterprise customers. Industry-leading uptime and performance demonstrate platform reliability. Cloudflare’s continued growth and innovation indicate strong long-term viability.
Perimeter 81: Simplified SASE Solution
Perimeter 81 focuses on easy-to-deploy SASE capabilities for small to medium-sized organizations. Their platform emphasizes simplicity and rapid implementation without sacrificing security effectiveness.
The solution particularly appeals to organizations seeking modern network security without the complexity typically associated with enterprise-grade platforms. Perimeter 81’s approach prioritizes user experience and administrative simplicity.
Security Capabilities: Next-generation firewall capabilities provide application control and threat prevention. Secure web gateway protects against web-based threats and enforces acceptable use policies. Zero Trust Network Access replaces traditional VPN complexity with modern authentication and authorization.
Scalability and Performance: Cloud-native architecture enables rapid scaling without hardware procurement. Global gateway network provides consistent performance for distributed organizations. However, the platform may have limitations for very large enterprise deployments.
Deployment and Management: Streamlined deployment process enables rapid implementation with minimal technical expertise. Intuitive management console simplifies policy configuration and ongoing administration. Self-service capabilities reduce dependency on specialized security personnel.
Integration Ecosystem: API support enables integration with common business applications and identity providers. However, the integration ecosystem may be less comprehensive than enterprise-focused alternatives. Organizations with complex integration requirements should carefully evaluate compatibility.
Pricing and Licensing: Transparent per-user pricing simplifies budgeting and procurement processes. No hidden fees or complex licensing tiers make cost prediction straightforward. Competitive pricing makes the platform accessible for smaller organizations with limited security budgets.
Vendor Support and Reliability: Responsive support team provides assistance during deployment and ongoing operations. Regular platform updates add new capabilities and address security vulnerabilities. The company’s growth trajectory suggests continued platform investment and development.
Juniper Networks: AI-Driven Network Security
Juniper Networks integrates artificial intelligence throughout their security platform to provide automated threat detection and response. Their Mist AI technology enhances both networking and security operations.
The platform combines traditional network security with modern cloud-delivered services. Juniper’s approach appeals to organizations seeking enterprise-grade capabilities with operational automation benefits.
Security Capabilities: SRX Series firewalls provide comprehensive threat prevention with machine learning-enhanced detection capabilities. Advanced threat protection includes sandboxing and behavioral analysis for sophisticated attack identification. Sky ATP cloud service delivers real-time threat intelligence updates.
Scalability and Performance: High-performance hardware platforms support demanding enterprise environments. Cloud-delivered security services enable rapid scaling without infrastructure constraints. Juniper supports diverse deployment models from branch offices to large data centers.
Deployment and Management: Security Director provides centralized management for policy deployment and monitoring. AI-driven automation reduces administrative overhead and improves security posture consistency. However, full platform optimization may require specialized expertise.
Integration Ecosystem: Open APIs and standard protocols support integration with diverse security ecosystems. Juniper’s networking heritage enables seamless integration with existing network infrastructure. Partner ecosystem provides additional integration options and specialized capabilities.
Pricing and Licensing: Enterprise licensing provides access to advanced features with predictable annual costs. However, premium capabilities may require higher-tier licensing which could increase total cost. Organizations should evaluate licensing requirements against actual feature usage.
Vendor Support and Reliability: Comprehensive support options include 24/7 technical assistance and proactive monitoring services. Juniper’s established market presence and continued innovation demonstrate long-term platform viability. Regular software updates enhance capabilities and address security vulnerabilities.
Detailed Feature Comparison Analysis
Comprehensive comparison requires examining specific capabilities across all evaluated platforms. This detailed analysis helps organizations identify solutions that best match their particular requirements and constraints.
Threat Prevention Capabilities: All platforms provide next-generation firewall functionality, but implementation approaches vary significantly. Fortinet’s custom ASICs deliver high-performance inspection, while cloud-native solutions like Zscaler leverage global threat intelligence and machine learning analytics.
Cloud Integration: Modern organizations require seamless cloud application protection and policy enforcement. Netskope excels in cloud application visibility and control, while Cloudflare provides edge-based protection for web applications and APIs. Traditional vendors like Cisco and Juniper offer cloud-delivered services alongside on-premises capabilities.
Zero Trust Implementation: Zero Trust architecture adoption drives platform selection decisions. Zscaler built their platform on Zero Trust principles from inception, while established vendors like Palo Alto alternatives retrofit existing architectures. Organizations should evaluate which approach better aligns with their security transformation goals.
Remote Access Capabilities: Modern workforce requirements demand secure remote access without traditional VPN limitations. Cato Networks and Perimeter 81 provide SASE-based remote access, while others offer VPN replacement solutions with varying degrees of integration and user experience optimization.
API and Automation Support: Security operations efficiency requires extensive automation and integration capabilities. All evaluated platforms provide API access, but depth and documentation quality vary. Organizations with complex automation requirements should evaluate API capabilities during proof-of-concept testing.
Compliance and Reporting: Regulatory compliance drives security platform selection for many organizations. Comprehensive logging, reporting, and audit trail capabilities are essential. Vendors differ in their compliance certifications and built-in reporting capabilities for various regulatory frameworks.
Implementation and Deployment Considerations
Successful security platform implementation requires careful planning and execution. Organizations must evaluate deployment complexity, resource requirements, and change management implications when selecting alternatives to Palo Alto Networks.
Technical Prerequisites: Each platform has specific infrastructure requirements and dependencies. Cloud-native solutions like Zscaler require reliable internet connectivity but minimal on-premises infrastructure. Traditional appliance-based solutions need hardware procurement, installation, and ongoing maintenance capabilities.
Staff Training Requirements: Security team capabilities significantly impact platform selection success. Complex platforms like Cisco require extensive training and certification programs. Simpler solutions like Perimeter 81 minimize training requirements but may offer fewer advanced capabilities.
Migration Strategies: Organizations must carefully plan migration from existing security platforms to minimize disruption. Phased deployment approaches reduce risk but extend implementation timelines. Parallel operations may be necessary during transition periods to ensure continuous protection.
Performance Testing: Proof-of-concept testing validates platform capabilities in real organizational environments. Load testing ensures solutions meet performance requirements under actual traffic conditions. User acceptance testing confirms that new platforms don’t negatively impact productivity or user experience.
Change Management: Security platform changes affect multiple organizational stakeholders including IT operations, security teams, and end users. Comprehensive change management programs ensure successful adoption and minimize resistance to new processes and procedures.
Rollback Planning: Implementation projects should include detailed rollback procedures in case of unexpected issues. Backup configurations and documented procedures enable rapid restoration of previous security postures if necessary.
Cost Analysis and Budget Planning
Total cost of ownership extends far beyond initial licensing fees. Organizations must evaluate comprehensive cost structures when comparing Palo Alto Networks alternatives to ensure accurate budget planning and ROI calculations.
Licensing Models: Vendors employ various licensing approaches including per-user subscriptions, traffic-based pricing, and appliance-based licenses. Subscription models provide predictable annual costs but may become expensive as organizations grow. Hardware-based licensing requires significant upfront investment but may offer better long-term economics for stable environments.
Infrastructure Costs: On-premises solutions require hardware procurement, data center space, power, and cooling infrastructure. Cloud-native alternatives eliminate these costs but may introduce dependency on reliable internet connectivity and potential bandwidth charges.
Professional Services: Complex platforms often require professional services for optimal deployment and configuration. Organizations should budget for consulting fees, training costs, and ongoing optimization services. Some vendors include basic professional services in their licensing while others charge separately.
Operational Expenses: Ongoing operational costs include staff time for administration, monitoring, and maintenance. Solutions with higher automation capabilities reduce operational overhead while complex platforms may require dedicated specialist staff.
Hidden Costs: Organizations should identify potential hidden costs including integration expenses, backup and disaster recovery requirements, and compliance audit support. Change management and user training costs often exceed initial estimates and should be included in budget planning.
ROI Considerations: Security platform value extends beyond cost reduction to include improved security posture, operational efficiency, and business enablement. Organizations should quantify benefits including reduced breach risk, faster incident response, and improved compliance capabilities.
Future-Proofing Your Security Investment
Security technology evolves rapidly, making future-proofing considerations critical for long-term platform success. Organizations must evaluate vendor roadmaps, technology trends, and architectural flexibility when selecting Palo Alto Networks alternatives.
Technology Roadmaps: Vendor development plans indicate future platform capabilities and strategic direction. Organizations should evaluate alignment between vendor roadmaps and their own technology evolution plans. Regular roadmap updates and customer input opportunities demonstrate vendor commitment to continued innovation.
AI and Machine Learning Integration: Artificial intelligence capabilities increasingly differentiate security platforms. Advanced analytics, automated threat detection, and self-healing capabilities reduce operational overhead while improving security effectiveness. Organizations should evaluate current AI capabilities and vendor plans for continued enhancement.
Cloud-Native Architecture: Digital transformation initiatives drive cloud adoption across all industries. Security platforms must seamlessly protect cloud workloads, applications, and data. Cloud-native architectures provide better scalability and integration compared to retrofitted legacy solutions.
API-First Development: Modern security operations require extensive automation and integration capabilities. Platforms designed with API-first principles enable better integration with security orchestration tools and custom automation workflows.
Compliance Evolution: Regulatory requirements continue evolving, particularly around data privacy and protection. Security platforms must adapt to new compliance requirements without requiring complete replacement. Vendor track records for compliance updates indicate future adaptation capabilities.
Vendor Stability: Long-term vendor viability affects platform investment protection. Organizations should evaluate vendor financial health, market position, and strategic partnerships. Acquisition risks and product discontinuation possibilities should factor into selection decisions.
| Platform | Security Capabilities | Scalability | Deployment | Pricing Model | Best For |
|---|---|---|---|---|---|
| Cato Networks | Integrated SASE, AI-driven threat detection | Global cloud infrastructure | Zero-touch provisioning | Subscription per location | Organizations seeking SASE simplification |
| Fortinet | Security Fabric, custom ASICs | Hardware-accelerated performance | Traditional appliance deployment | Hardware + subscription | High-performance enterprise environments |
| Zscaler | Zero Trust Exchange, cloud-native | Infinite cloud scalability | Agent-based, cloud-delivered | User-based subscription | Cloud-first, remote workforce |
| Netskope | Data-centric protection, advanced DLP | Global NewEdge network | Multiple deployment options | User and feature-based | Organizations with extensive cloud app usage |
| Versa Networks | SD-WAN integrated security | Software-defined scalability | Branch office optimization | Bundled networking + security | Distributed enterprises with SD-WAN needs |
| Cisco | SecureX integration, Talos intelligence | Enterprise-grade hardware | Complex, requires expertise | Enterprise licensing | Large enterprises with Cisco infrastructure |
| Cloudflare | Edge-based protection, WAF, bot management | Global anycast network | DNS-based activation | Usage-based with tiers | Web application and API protection |
| Perimeter 81 | Simplified SASE, Zero Trust | Cloud-native, moderate scale | Easy deployment, self-service | Per-user subscription | SMB organizations seeking simplicity |
| Juniper Networks | Mist AI, advanced threat protection | Enterprise hardware platforms | Traditional with AI automation | Hardware + software licensing | AI-driven security operations |
Making the Right Choice for Your Organization
Selecting the optimal Palo Alto Networks alternative requires careful alignment between organizational needs and platform capabilities. No single solution provides the best fit for every use case, making thorough evaluation essential for long-term success.
Organizational Assessment: Begin with comprehensive analysis of current security requirements, infrastructure constraints, and future growth plans. Document existing pain points with current solutions and prioritize improvement areas. This foundation guides platform evaluation and selection criteria.
Stakeholder Alignment: Successful platform selection requires input from security teams, IT operations, business units, and executive leadership. Each stakeholder group brings different perspectives and requirements that must be balanced in the final decision.
Proof of Concept Testing: Hands-on evaluation validates vendor claims and demonstrates platform capabilities in real organizational environments. Design comprehensive test scenarios that reflect actual use cases and performance requirements. Include both technical testing and user experience evaluation.
Risk Assessment: Evaluate implementation risks including technical complexity, resource requirements, and potential disruption. Consider vendor stability, support quality, and long-term viability. Develop mitigation strategies for identified risks before proceeding with implementation.
Decision Framework: Establish clear evaluation criteria with weighted scoring based on organizational priorities. This structured approach enables objective comparison between alternatives and supports decision documentation and communication.
Conclusion
The network security landscape offers compelling alternatives to Palo Alto Networks across diverse organizational needs and requirements. From cloud-native SASE solutions like Cato Networks and Zscaler to performance-optimized platforms like Fortinet, each alternative provides unique strengths for specific use cases.
Successful platform selection requires thorough evaluation of security capabilities, scalability requirements, deployment complexity, and total cost of ownership. Organizations must balance current needs with future requirements while considering vendor stability and technology roadmaps. With careful assessment and structured comparison, security teams can identify solutions that deliver superior value and effectiveness for their specific environments.
Frequently Asked Questions About Palo Alto Networks Alternatives
- Which Palo Alto Networks alternative offers the best cost-effectiveness?
Fortinet typically provides the best price-performance ratio for high-throughput environments, while Perimeter 81 offers competitive pricing for small to medium organizations. Cost-effectiveness depends on specific requirements including throughput needs, feature requirements, and deployment preferences. - What is the best cloud-native alternative to Palo Alto Networks?
Zscaler leads in cloud-native security with their Zero Trust Exchange platform built specifically for cloud-first organizations. Cato Networks also provides comprehensive cloud-native SASE capabilities with integrated networking and security functions. - Which alternative provides the easiest migration from Palo Alto Networks?
Cisco offers the most familiar deployment model for organizations comfortable with traditional appliance-based security. However, cloud-native solutions like Cloudflare provide rapid deployment with minimal infrastructure changes. - What are the key differences between SASE platforms and traditional firewall alternatives?
SASE platforms like Cato Networks and Versa Networks integrate networking and security functions into unified cloud services, while traditional alternatives like Fortinet and Juniper focus primarily on advanced firewall capabilities with separate networking components. - Which Palo Alto Networks alternative offers the best AI and automation capabilities?
Juniper Networks leads in AI integration with their Mist AI technology, while Zscaler provides extensive machine learning-driven threat detection. Both platforms offer significant automation capabilities that reduce operational overhead. - How do these alternatives compare for remote workforce security?
Zscaler excels for remote workforce protection with agent-based deployment and cloud-delivered security. Perimeter 81 provides simplified remote access for smaller organizations, while Cato Networks offers comprehensive SASE capabilities including Zero Trust Network Access. - What should organizations consider when evaluating vendor lock-in risks?
Evaluate API availability, data export capabilities, and standards compliance for each platform. Cloud-native solutions may create dependency on specific vendors, while open standards-based platforms provide more flexibility for future changes. - Which alternative provides the best integration with existing security tools?
Cisco offers extensive integration capabilities with their SecureX platform and large partner ecosystem. Fortinet’s Security Fabric also provides comprehensive third-party integration support through their Open Ecosystem initiative.
References:
















 Stack Insight is intended to support informed decision-making by providing independent information about business software and services. Some product details, including pricing, features, and promotional offers, may be supplied by vendors or partners and can change without notice.
Stack Insight is intended to support informed decision-making by providing independent information about business software and services. Some product details, including pricing, features, and promotional offers, may be supplied by vendors or partners and can change without notice.