The Complete Guide to Palo Alto Networks Competitors: Top 10 Network Security Solutions for 2026
The cybersecurity landscape continues evolving rapidly as organizations face increasingly sophisticated threats. Palo Alto Networks has established itself as a leading player in the network security space, offering comprehensive next-generation firewall (NGFW) solutions and advanced threat protection. However, many businesses seek alternatives that might better fit their specific requirements, budget constraints, or operational environments.
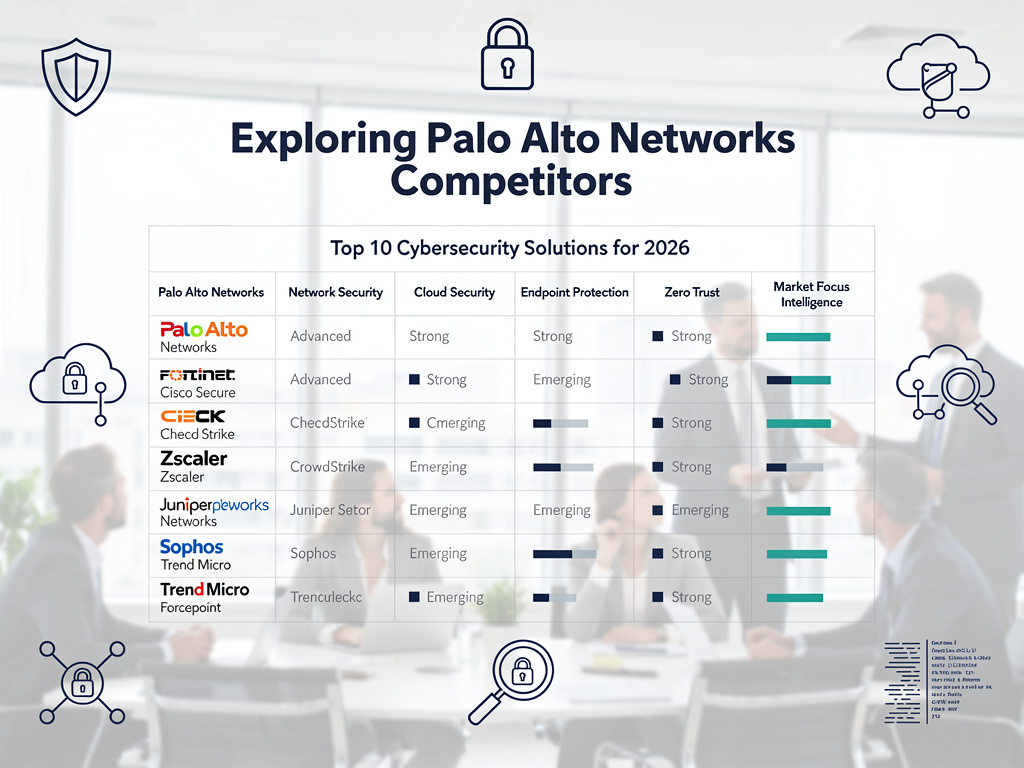
This comprehensive guide examines the top 10 Palo Alto Networks competitors and alternatives available in 2026. Each solution offers unique strengths across different deployment scenarios, from cloud-native architectures to traditional on-premises environments. Organizations evaluating network security platforms must consider factors including performance, scalability, ease of management, integration capabilities, and total cost of ownership when making their selection.
Understanding the Network Security Landscape
The network security market has transformed dramatically over the past decade. Traditional perimeter-based security models are giving way to more sophisticated approaches that accommodate cloud computing, remote work, and zero-trust architectures.
Modern security platforms must address several key challenges:
- Advanced persistent threats (APTs) that bypass traditional defenses
- Hybrid cloud environments requiring consistent security policies
- Remote workforce protection without compromising user experience
- Compliance requirements across multiple regulatory frameworks
- Integration with existing security orchestration and automation tools
Organizations are increasingly seeking solutions that provide comprehensive visibility, automated threat response, and simplified management across distributed infrastructures. The competitive landscape reflects this shift, with vendors offering everything from specialized cloud security platforms to integrated security suites.
Evaluation Criteria for Network Security Solutions
Before diving into specific vendor analysis, it’s essential to establish clear evaluation criteria. These benchmarks help organizations make informed decisions based on their unique requirements rather than marketing promises.
Performance and Scalability
Network security solutions must handle increasing traffic volumes without becoming performance bottlenecks. Throughput capabilities, latency impact, and horizontal scaling options are critical considerations. Solutions should maintain consistent performance across different traffic types and attack scenarios.
Threat Detection and Prevention
Advanced threat protection capabilities distinguish modern security platforms from legacy firewalls. Machine learning algorithms, behavioral analysis, and threat intelligence integration determine how effectively solutions identify and block sophisticated attacks.
Management and Usability
Complex security platforms often fail due to operational challenges rather than technical limitations. Intuitive management interfaces, centralized policy control, and automated workflows significantly impact deployment success and ongoing effectiveness.
Integration and Ecosystem
No security solution operates in isolation. API availability, third-party integrations, and compatibility with existing security tools affect overall security posture and operational efficiency.
Cost and Licensing
Total cost of ownership extends beyond initial licensing fees. Deployment costs, ongoing maintenance, training requirements, and scaling expenses must factor into financial evaluations.
Fortinet: Enterprise-Grade Security at Scale
Fortinet has emerged as one of the strongest Palo Alto Networks alternatives, particularly for large enterprises requiring high-performance security solutions. The company’s FortiGate next-generation firewalls leverage custom ASIC processors to deliver industry-leading throughput while maintaining comprehensive security inspection.
Fortinet’s Core Strengths
Performance Leadership: Fortinet’s custom Security Processing Units (SPUs) enable wire-speed performance across all security features. Unlike software-based solutions that compromise performance when advanced features are enabled, FortiGate appliances maintain consistent throughput regardless of security policy complexity.
The FortiOS operating system provides unified security management across the entire Fortinet Security Fabric ecosystem. This integration enables coordinated threat response across network, endpoint, cloud, and application security components.
Comprehensive Security Services: Fortinet offers extensive security services including intrusion prevention, application control, web filtering, antimalware, and SSL inspection. The FortiGuard threat intelligence service provides real-time updates based on global threat research and machine learning analysis.
Deployment Flexibility
Fortinet supports diverse deployment scenarios through physical appliances, virtual machines, cloud instances, and container-based implementations. FortiGate-VM instances are available across major cloud platforms including AWS, Azure, and Google Cloud Platform.
The company’s SD-WAN capabilities integrate seamlessly with security functions, enabling organizations to consolidate networking and security infrastructure. This convergence reduces complexity while improving performance for distributed organizations.
Competitive Positioning
Compared to Palo Alto Networks, Fortinet typically offers better price-performance ratios, especially for high-throughput deployments. Organizations with significant bandwidth requirements often find Fortinet solutions more cost-effective without sacrificing security effectiveness.
However, Fortinet’s management interface can be more complex than Palo Alto’s intuitive Panorama platform. Organizations with limited security expertise may require additional training or professional services support.
Cisco: Networking Giant’s Security Evolution
Cisco’s security portfolio has evolved significantly beyond traditional firewalls to encompass comprehensive threat protection across networks, clouds, and endpoints. The company leverages its dominant networking position to deliver integrated security solutions that many organizations find compelling.
Cisco’s Security Architecture
Firepower Next-Generation Firewalls: Cisco’s Firepower NGFW platform combines traditional firewall capabilities with advanced malware protection, intrusion prevention, and application visibility. The solution integrates with Cisco’s broader security ecosystem including Umbrella cloud security and Talos threat intelligence.
Cisco’s approach emphasizes security integration across the entire network infrastructure. Switches, routers, and wireless access points can participate in threat detection and response, creating a comprehensive security mesh throughout the organization.
Cloud and Zero-Trust Capabilities
Cisco Umbrella provides cloud-delivered security services including DNS filtering, web security, and cloud access security broker (CASB) functionality. This cloud-first approach aligns well with organizations adopting software-as-a-service applications and cloud infrastructure.
The company’s zero-trust architecture leverages identity integration, device posture assessment, and micro-segmentation to implement granular access controls. Cisco’s Identity Services Engine (ISE) provides centralized policy management across wired, wireless, and VPN connections.
Strengths and Considerations
Cisco’s primary advantage lies in its comprehensive networking and security integration. Organizations already invested in Cisco infrastructure can achieve better visibility and control by extending their existing investments rather than introducing disparate security vendors.
The company’s global support organization and extensive partner ecosystem provide implementation and ongoing support advantages, particularly for complex enterprise deployments requiring professional services assistance.
However, Cisco’s licensing models can be complex and expensive, particularly for organizations requiring advanced security features across large deployments. The company’s acquisition-driven portfolio sometimes lacks the cohesive integration found in purpose-built security platforms.
Zscaler: Cloud-Native Security Pioneer
Zscaler revolutionized network security by delivering comprehensive protection through a global cloud platform rather than traditional appliance-based deployments. This cloud-native approach appeals to organizations embracing digital transformation and seeking to eliminate network security hardware.
Zero-Trust Architecture
Cloud-Delivered Security: Zscaler’s platform processes billions of transactions daily through strategically located data centers worldwide. This global infrastructure enables consistent security policy enforcement regardless of user location or network connection method.
The platform’s zero-trust approach treats every connection as untrusted, requiring authentication and authorization before granting access to applications or resources. This model aligns well with modern workforce mobility and cloud application adoption trends.
Performance and User Experience
Zscaler’s global points of presence ensure minimal latency impact while providing comprehensive security inspection. The platform’s traffic optimization includes SSL certificate management, content caching, and bandwidth optimization to improve overall user experience.
Application-Centric Policies: Rather than relying solely on network-level controls, Zscaler enables granular application-level policies based on user identity, device posture, and contextual factors. This approach provides better security with improved user productivity.
Competitive Analysis
Compared to Palo Alto Networks’ traditional appliance-based approach, Zscaler eliminates hardware management, capacity planning, and infrastructure scaling challenges. Organizations can rapidly deploy global security policies without physical infrastructure investments.
However, Zscaler’s cloud-only model may not suit organizations with strict data sovereignty requirements or those preferring on-premises security inspection for sensitive traffic. The platform’s effectiveness depends heavily on internet connectivity quality and redundancy.
Netskope: Cloud Access Security Excellence
Netskope specializes in cloud access security broker (CASB) and secure web gateway (SWG) capabilities, making it a strong alternative for organizations prioritizing cloud application security and data protection.
Cloud Security Expertise
Data Loss Prevention: Netskope’s platform provides comprehensive data loss prevention (DLP) capabilities across cloud applications, web traffic, and file sharing services. The solution uses machine learning and content inspection to identify sensitive data and enforce appropriate protection policies.
The company’s cloud application risk assessment provides detailed visibility into sanctioned and unsanctioned cloud services usage. Organizations can implement granular policies based on application risk scores, compliance requirements, and business needs.
Advanced Threat Protection
Netskope’s threat protection capabilities include malware detection, command and control communication blocking, and behavioral analysis for identifying compromised accounts or insider threats.
API-Based Protection: Unlike proxy-based solutions that may impact performance, Netskope offers API-based protection for major cloud platforms including Office 365, Google Workspace, and Salesforce. This approach provides comprehensive security without affecting user experience.
Deployment and Integration
Netskope supports multiple deployment options including forward proxy, reverse proxy, API integration, and endpoint client installation. This flexibility enables organizations to implement appropriate protection methods for different use cases and user populations.
The platform integrates with major identity providers, SIEM systems, and security orchestration tools to provide coordinated threat response and comprehensive security analytics.
Cato Networks: SASE Platform Innovation
Cato Networks pioneered the Secure Access Service Edge (SASE) category by converging networking and security functions into a unified cloud platform. This innovative approach appeals to organizations seeking to simplify their network and security architecture.
Converged Platform Architecture
Network and Security Convergence: Cato’s platform combines SD-WAN, secure web gateway, firewall, intrusion prevention, and other security functions into a single cloud service. This convergence eliminates the complexity of managing separate networking and security vendors.
The company’s global backbone network provides optimized connectivity between branch offices, cloud resources, and mobile users while applying consistent security policies across all connections.
Simplified Management
Cato’s management interface provides unified visibility and control across networking and security functions. Organizations can implement changes globally through a single console rather than managing multiple point solutions.
Zero-Touch Deployment: Branch office connectivity requires only installing Cato’s socket device, which automatically establishes secure connections to the cloud platform. This approach significantly reduces deployment complexity and ongoing maintenance requirements.
Market Positioning
Compared to Palo Alto Networks’ appliance-centric approach, Cato offers superior deployment simplicity and reduced operational overhead. Organizations with distributed branch networks particularly benefit from Cato’s cloud-delivered model.
However, Cato’s relatively newer market presence may concern organizations preferring established vendors with extensive track records. The platform’s performance depends on internet connectivity quality and geographic proximity to Cato’s points of presence.
Cloudflare: Global Network Security
Cloudflare has expanded beyond content delivery and DDoS protection to offer comprehensive network security services through its global edge network. This unique positioning provides both performance and security benefits for internet-facing applications and services.
Edge Security Services
Web Application Firewall: Cloudflare’s WAF protects web applications from OWASP Top 10 vulnerabilities, bot attacks, and application-layer DDoS attempts. The service leverages machine learning and threat intelligence from Cloudflare’s vast network to provide real-time protection.
The company’s Zero Trust Access solution enables secure remote access to internal applications without traditional VPN complexity. Users connect through Cloudflare’s edge network, which applies identity verification and security policies before granting access.
Performance Integration
Unlike standalone security solutions that may impact performance, Cloudflare’s security services are integrated with content delivery and network optimization functions. Organizations often experience improved performance while gaining enhanced security protection.
DNS Security: Cloudflare for Teams includes DNS filtering, malware protection, and phishing prevention through the company’s 1.1.1.1 resolver infrastructure. This approach provides security protection regardless of user location or network connection.
Competitive Considerations
Cloudflare’s global network provides unmatched scale and geographic coverage compared to traditional security vendors. Organizations with international operations benefit from consistent security protection and performance optimization worldwide.
However, Cloudflare’s security offerings may not provide the deep packet inspection and advanced threat analysis capabilities found in dedicated NGFW platforms. The solution works best as part of a layered security strategy rather than a complete replacement for traditional firewalls.
Perimeter 81: Secure Remote Access Focus
Perimeter 81 addresses the growing need for secure remote access and zero-trust network security, particularly for organizations with distributed workforces and cloud-first architectures.
Zero-Trust Network Access
Software-Defined Perimeter: Perimeter 81’s platform creates encrypted micro-tunnels between users and resources, implementing zero-trust principles without requiring major infrastructure changes. This approach provides granular access control while maintaining user experience.
The solution includes integrated threat protection, malware scanning, and web filtering to protect remote users from internet-based threats. Organizations can implement consistent security policies regardless of user location or network connection method.
Cloud-Native Deployment
Perimeter 81’s cloud-native architecture eliminates the need for physical appliances or complex VPN infrastructure. Organizations can deploy secure access policies globally within minutes rather than weeks required for traditional solutions.
Identity Integration: The platform integrates with major identity providers including Active Directory, Okta, and Azure AD to leverage existing authentication systems and provide single sign-on capabilities.
Market Focus
Perimeter 81 targets small to medium-sized businesses and distributed organizations that may find traditional enterprise security platforms too complex or expensive. The solution’s simplicity and cloud-delivered model appeal to organizations with limited IT security expertise.
Compared to Palo Alto Networks’ comprehensive platform, Perimeter 81 offers easier deployment and management but may lack advanced threat protection and network visibility features required by larger enterprises.
Juniper Networks: AI-Driven Security
Juniper Networks combines advanced networking expertise with artificial intelligence to deliver security solutions that adapt to evolving threats and network conditions automatically.
AI-Powered Threat Detection
Mist AI Integration: Juniper’s security platforms leverage Mist AI to provide automated threat detection, anomaly identification, and predictive security analytics. This AI-driven approach enables proactive threat response rather than reactive protection.
The company’s Connected Security platform provides coordinated threat response across network, endpoint, and cloud security components. Machine learning algorithms continuously analyze traffic patterns to identify subtle indicators of compromise.
Network Integration Advantages
Juniper’s security solutions integrate seamlessly with the company’s switching and routing platforms to provide comprehensive network visibility and control. Organizations can implement micro-segmentation and automated threat response across the entire network infrastructure.
SRX Series Firewalls: Juniper’s SRX next-generation firewalls provide high-performance threat protection with integrated intrusion prevention, application visibility, and advanced malware protection. The solutions scale from branch office deployments to data center installations.
Operational Excellence
Juniper emphasizes operational simplicity through AI-driven automation and self-healing network capabilities. The company’s Contrail Security platform provides micro-segmentation and automated policy enforcement for cloud and virtualized environments.
Compared to Palo Alto Networks, Juniper often provides better integration with existing network infrastructure and more advanced automation capabilities. However, the company’s security market presence is smaller than dedicated security vendors.
Versa Networks: SD-WAN Security Integration
Versa Networks specializes in secure SD-WAN solutions that integrate networking and security functions for distributed enterprise deployments.
Converged SD-WAN Platform
Security-First SD-WAN: Versa’s platform integrates next-generation firewall, intrusion prevention, web filtering, and advanced threat protection with SD-WAN networking functions. This convergence reduces complexity while providing comprehensive branch office protection.
The solution includes cloud security services for protecting SaaS applications and internet traffic without requiring separate security appliances or cloud gateways.
Multi-Tenant Capabilities
Versa’s platform supports multi-tenant deployments, enabling managed service providers and large enterprises to implement granular policy isolation and management across different organizations or business units.
Analytics and Visibility: The platform provides comprehensive analytics across networking and security functions, enabling organizations to identify performance issues, security threats, and optimization opportunities through unified dashboards.
Competitive Position
Versa Networks targets organizations seeking to consolidate branch office networking and security infrastructure. The solution provides better price-performance ratios than deploying separate SD-WAN and security appliances.
However, Versa’s market presence is smaller than established security vendors, which may concern organizations requiring extensive support and professional services capabilities.
Comparative Analysis and Decision Framework
Selecting the right Palo Alto Networks alternative requires careful consideration of organizational requirements, existing infrastructure, and future growth plans. Each competitor offers distinct advantages across different deployment scenarios and use cases.
Performance and Scalability Comparison
| Vendor | Throughput Leadership | Scalability Model | Performance Impact |
|---|---|---|---|
| Fortinet | Industry-leading ASIC performance | Hardware scaling | Minimal with all features enabled |
| Cisco | Strong enterprise performance | Modular appliances | Varies by platform |
| Zscaler | Cloud-scale processing | Automatic cloud scaling | Depends on connectivity |
| Netskope | Cloud-optimized | Global cloud platform | Minimal for API protection |
| Cato Networks | Global backbone optimization | Cloud-native scaling | Network optimization included |
Security Effectiveness Assessment
Advanced threat protection capabilities vary significantly across vendors. Organizations must evaluate detection accuracy, false positive rates, and response automation when comparing solutions.
Machine Learning Integration: Vendors like Juniper and Zscaler emphasize AI-driven threat detection, while others focus on signature-based and heuristic analysis methods. The effectiveness depends on threat landscape evolution and organizational security expertise.
Total Cost of Ownership Analysis
Initial licensing costs represent only a portion of total ownership expenses. Organizations must consider deployment costs, training requirements, ongoing maintenance, and scaling expenses when evaluating alternatives.
- Hardware-based solutions require ongoing maintenance, power, cooling, and replacement planning
- Cloud-delivered platforms eliminate infrastructure costs but may have higher per-user licensing fees
- Professional services requirements vary significantly based on solution complexity and organizational expertise
- Training costs depend on how significantly new platforms differ from existing security tools
Implementation and Migration Strategies
Successfully transitioning from Palo Alto Networks to alternative solutions requires careful planning and phased implementation approaches. Organizations must maintain security effectiveness while minimizing operational disruption.
Risk Mitigation Approaches
Parallel Deployment: Many organizations implement new security solutions alongside existing Palo Alto equipment during transition periods. This approach enables comprehensive testing and gradual migration without creating security gaps.
Proof-of-concept deployments in non-critical environments allow security teams to evaluate performance, management complexity, and integration capabilities before committing to full-scale implementations.
Policy Migration Considerations
Security policy translation between platforms often requires significant effort and careful validation. Organizations should audit existing policies to identify redundant or outdated rules before migration.
Testing and Validation: Comprehensive testing across different traffic types, attack scenarios, and performance conditions ensures that new solutions provide equivalent or better protection than existing deployments.
Training and Change Management
Security team training requirements vary based on solution complexity and similarity to existing tools. Organizations should factor training costs and transition periods into implementation timelines.
Change management processes must address both technical and operational aspects of platform transitions. Clear communication about benefits, timelines, and support resources helps ensure successful adoption.
Future Trends and Considerations
The network security market continues evolving rapidly as organizations adapt to changing threat landscapes, technology trends, and business requirements. Understanding these trends helps organizations select solutions that will remain relevant and effective long-term.
Cloud and Hybrid Architecture Support
Organizations increasingly adopt multi-cloud strategies requiring consistent security policies across different cloud platforms and on-premises environments. Solutions must provide unified management and policy enforcement regardless of deployment location.
Container and Kubernetes Security: As containerized applications become mainstream, network security platforms must provide appropriate visibility and control for dynamic, ephemeral workloads.
Zero-Trust Evolution
Zero-trust architectures continue maturing beyond initial identity verification to include device posture assessment, behavioral analysis, and continuous risk evaluation. Security platforms must evolve to support these advanced implementation models.
Integration with identity providers, endpoint detection and response tools, and cloud access security brokers becomes increasingly important for comprehensive zero-trust implementations.
Artificial Intelligence Integration
Machine learning and artificial intelligence capabilities will become standard features rather than competitive differentiators. Organizations should evaluate how vendors collect training data, update models, and provide transparency into AI-driven decisions.
Automation and Orchestration: Security operations teams face increasing alert volumes and complexity. Platforms must provide intelligent automation and integration with security orchestration tools to maintain effectiveness with existing resources.
The competitive landscape will continue evolving as vendors adapt to these trends. Organizations should prioritize solutions with strong development roadmaps and commitment to emerging technology integration rather than focusing solely on current capabilities.
Conclusion
The network security market offers numerous viable alternatives to Palo Alto Networks, each with distinct strengths across different deployment scenarios and organizational requirements. Fortinet leads in performance and enterprise scalability, while Zscaler pioneers cloud-native security delivery. Cisco provides comprehensive integration for networking-centric organizations, and emerging players like Cato Networks offer innovative SASE platforms. Success depends on carefully matching vendor capabilities with specific business requirements, existing infrastructure, and future strategic directions rather than selecting based solely on market reputation or pricing considerations.
Frequently Asked Questions About Palo Alto Networks Competitors
Which Palo Alto Networks competitor offers the best performance for high-throughput environments?
Fortinet typically leads in raw performance metrics due to their custom ASIC processors. FortiGate appliances maintain wire-speed performance even with all security features enabled, making them ideal for high-bandwidth environments like data centers and internet gateways.
What are the most cost-effective alternatives to Palo Alto Networks for small businesses?
Perimeter 81 and Cloudflare offer cloud-delivered security services that eliminate hardware costs and provide subscription-based pricing models suitable for smaller organizations. These solutions require minimal IT expertise and can be deployed quickly without significant upfront investments.
Which competitors provide the best cloud security capabilities?
Zscaler and Netskope specialize in cloud security, offering comprehensive CASB and secure web gateway capabilities. Zscaler excels in zero-trust access, while Netskope provides superior data loss prevention and cloud application risk assessment features.
How do licensing models compare between Palo Alto Networks alternatives?
Licensing varies significantly across vendors. Fortinet and Cisco typically use appliance-based licensing with annual subscriptions for security services. Cloud providers like Zscaler and Cato use per-user models, while Cloudflare offers bandwidth-based pricing for many services.
What integration challenges should organizations expect when migrating from Palo Alto Networks?
Policy migration requires careful translation and testing across platforms. API integrations with SIEM and orchestration tools may need reconfiguration. Staff training requirements vary based on solution complexity and interface similarities to existing Palo Alto management tools.
Which Palo Alto Networks competitors offer the best management simplicity?
Cato Networks and Perimeter 81 emphasize management simplicity through cloud-delivered platforms and unified interfaces. These solutions reduce operational complexity compared to traditional appliance-based deployments requiring separate management systems.
How do support and professional services compare across different vendors?
Cisco and Fortinet offer extensive global support organizations and partner ecosystems. Newer vendors like Cato Networks and Perimeter 81 provide direct support but may have limited professional services capabilities for complex enterprise deployments.
What deployment timeframes should organizations expect for different alternatives?
Cloud-delivered solutions like Zscaler and Cato Networks can be deployed within days or weeks. Traditional appliance-based alternatives typically require several weeks to months depending on hardware procurement, configuration complexity, and testing requirements.
References:
Gartner Reviews – Palo Alto Networks Alternatives
Check Point – Palo Alto Networks Alternatives Comparison

















 Stack Insight is intended to support informed decision-making by providing independent information about business software and services. Some product details, including pricing, features, and promotional offers, may be supplied by vendors or partners and can change without notice.
Stack Insight is intended to support informed decision-making by providing independent information about business software and services. Some product details, including pricing, features, and promotional offers, may be supplied by vendors or partners and can change without notice.